Pennsylvania Clean Energy Employment surges, highlighting workforce growth in energy efficiency, solar, wind, grid and storage, and alternative transportation, supporting COVID-19 recovery, high-wage jobs, manufacturing, construction, and statewide economic resilience.
Key Points
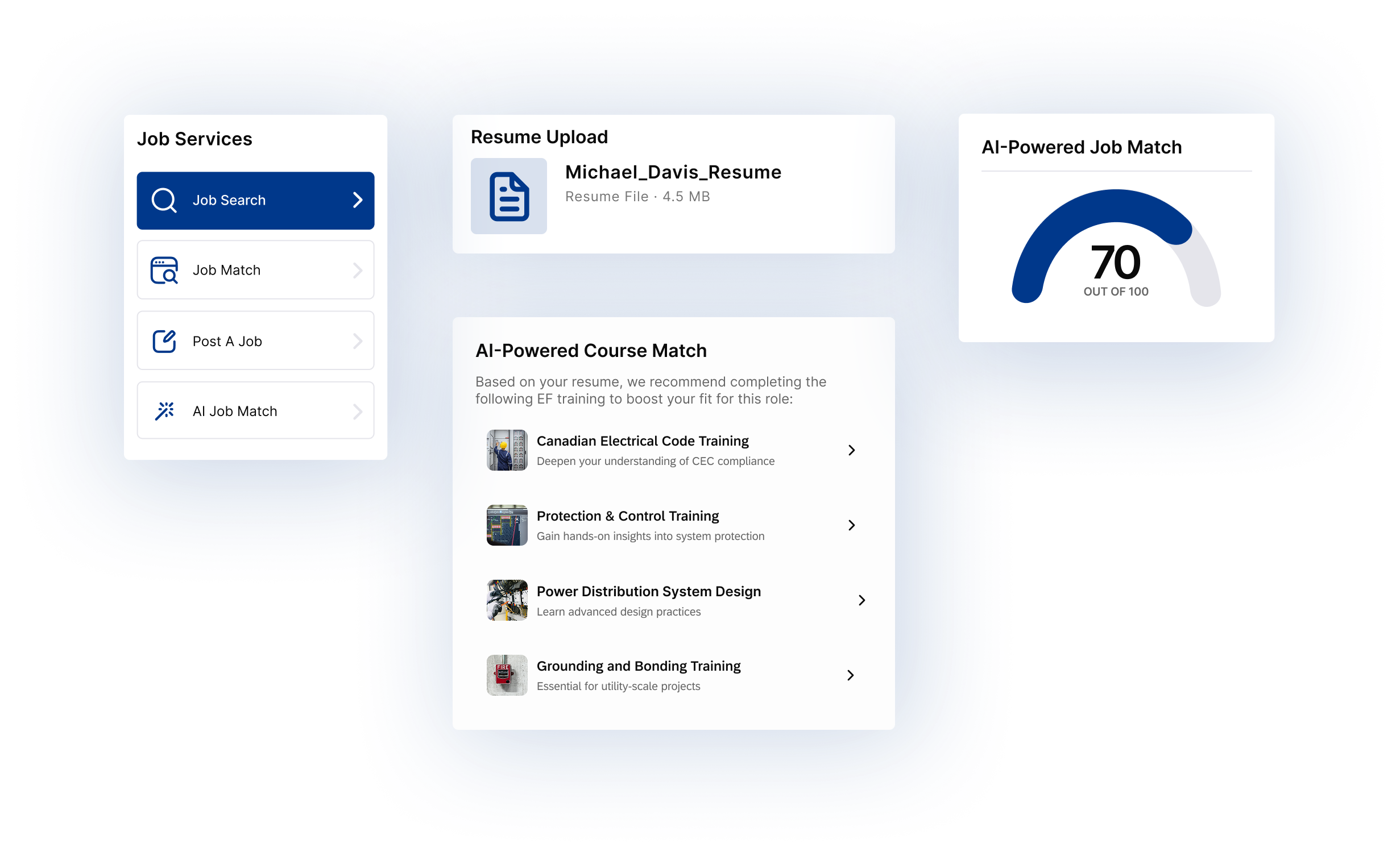
Jobs across clean power, efficiency, grid, storage, and advanced transport fueling Pennsylvania's workforce growth.
✅ 8.7% job growth from 2017-2019, outpacing statewide average
✅ 97,000+ employed across efficiency, solar, wind, grid, and fuels
✅ 75% earn above median; strong full-time opportunities
The 2020 Pennsylvania Clean Energy Employment Report has been released, and Gov. Tom Wolf is energized by it.
This "comes at an opportune time, as government and industry leaders look to strengthen Pennsylvania's workforce and economy in response to the challenges of the COVID-19 pandemic," Wolf said Monday in a prepared statement. "This detailed analysis of data and trends in clean energy employment ... demonstrates the sector was a top job generator statewide, and shows which industries were hiring and looking for trained workers."
Foremost among the findings, released Monday, is that the clean energy sector was responsible for adding 7,794 jobs from 2017 through 2019. That is an 8.7% average job growth rate, well above the 1.9% overall average in the state, according to a news release from Wolf's office.
This report lists employment data in five industries: energy efficiency; clean energy generation; alternative transportation; clean grid and storage; and clean fuels, while some cleaner states still import dirty electricity in regional markets.
The energy efficiency industry was the biggest clean energy employer in the state last year, with more than 71,400 state residents working in construction, technology and manufacturing jobs related to energy-efficient systems.
Solar energy workers comprised the largest share of the clean energy generation workforce – 35.4%, or 5,173 individuals. Solar employment increased 8.3% from 2017 to 2019, while there was a slight decline nationwide amid clean energy job losses reported in May.
Wind energy firms employed 2,937, and policy moves such as Ontario's clean electricity regulations signal broader market shifts, with more than 21% of those roles in manufacturing.
Job losses, though, were recorded in nuclear generation (minus 4.5%) and coal generation (minus 8.6%) over the two-year period, as electricity deregulation remains a point of debate in the sector. This mirrors national declines in both categories.
Federal efforts to support coal community revitalization are channeling clean energy projects to hard-hit regions.
Natural gas electric generation capacity doubled across Pennsylvania over the past decade; even as residents could face winter electricity price increases according to recent reports, employment still grew 13.4% from 2017 through 2019. But increasing output from unconventional wells has outpaced demand, sparking reductions in siting and drilling for new wells.
The Clean Energy Employment Report was released along with – and as part of – the 2020 Pennsylvania Energy Employment Report, which asserts that energy remains a large employer in the state, and new clean energy funding announcements underscore the sector's momentum. As of the last quarter of 2019, according to the larger report, energy accounted for 269,031 jobs, or 4.5% of the overall statewide workforce.
Wolf, in summary, said: "This report shows that workforce training investment decisions can benefit Pennsylvanians right now and position the state going forward to grow and improve livelihoods, the economy and our environment."
Related News