SCADA Architecture
By Frank Baker, Associate Editor
By Frank Baker, Associate Editor
SCADA architecture governs RTUs, PLCs, HMI servers, communication networks, and cybersecurity segmentation to preserve deterministic switching and validated system state across transmission and distribution control operations.
SCADA architecture determines whether supervisory telemetry becomes enforceable control authority or delayed situational awareness. In transmission and distribution operations, the structure of the control layers determines how quickly breaker status, voltage deviations, and fault events propagate into switching decisions.
When feeders host high DER penetration, automated reclosers, and dense sensor endpoints, architectural latency and segmentation design directly influence stability. If topology updates arrive out of sequence or fail to synchronize across servers, the operator does not lose data first. The operator loses confidence in the system state.
Control rooms operate within tolerance boundaries. When state estimation drift exceeds defined thresholds, typically beyond one second for breaker status validation in high-speed automation environments, automated switching can execute against outdated topology.
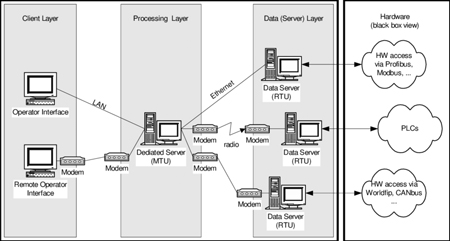
SCADA architecture is not an IT layout. It is a deterministic control boundary composed of field acquisition, communication transport, supervisory processing, and operator visualization. Each layer must preserve timing discipline and segmented trust without introducing ambiguity.
At the field layer, RTUs and PLCs acquire analog and digital signals. Polling intervals, event driven reporting, and time stamping protocols determine whether telemetry remains sequence consistent during disturbances. During feeder fault storms, event volumes can increase by up to 5 times nominal rates. Architecture must sustain this surge without buffer overflow or packet loss.
A foundational understanding of system roles begins with What is SCADA, but architecture governs how those components behave under stress.

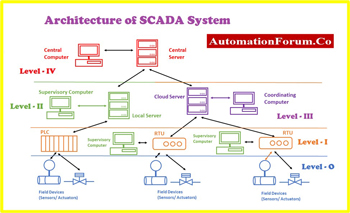
A SCADA system is composed of coordinated system components, including remote terminal units, programmable logic controllers, human-machine interface HMI servers, and supervisory control software applications operating across real-time communication networks. Architecture determines how input and outputs are validated, how SCADA protocols enforce deterministic messaging, and how quality of service constraints prevent latency from corrupting state synchronization in large-scale transmission and distribution environments.
Communication topology shapes resilience. Star networks centralize traffic but increase single point dependency. Ring or mesh designs improve survivability yet introduce synchronization complexity.
Utilities deploying Smart Grid Communication frameworks must enforce deterministic routing and latency control. If communication jitter exceeds operational tolerance, state changes may register inconsistently across supervisory nodes.
In substations, distributed intelligence enabled by Substation SCADA enables localized autonomy. However, local autonomy introduces governance tradeoffs. Firmware divergence or misaligned configuration between substations can fragment system behavior during restoration events.
Edge deployments such as Smart Grid Edge Computing reduce backhaul dependency but increase lifecycle management complexity. Quarterly patch cycles rarely align with real time threat exposure.
In feeders with high inverter based DER penetration, harmonic distortion can distort analog measurements at the RTU layer if sampling filters are misaligned with supervisory aggregation intervals. The result is not data loss. It is false validation of unstable voltage conditions that appear within tolerance until switching logic executes.
Supervisory servers aggregate telemetry into a coherent operational model. Database replication, failover configuration, and redundancy logic determine whether the system maintains a validated state during server transitions.
If topology timestamps diverge across redundant servers beyond defined tolerance, supervisory control must invalidate automation pathways rather than continue execution under degraded confidence. Continuing under silent drift is not resilience. It is unverified control authority. In high speed feeder automation environments, event ordering must remain deterministic within sub 100 millisecond resolution to prevent replay ambiguity across redundant nodes.
Model confidence is not binary. If telemetry freshness exceeds tolerance, typically beyond two polling intervals, the supervisory model should degrade visibly rather than silently. Silent degradation creates false certainty.
Integration boundaries must be carefully controlled. SCADA Integration connects supervisory systems to outage management, analytics platforms, and enterprise dashboards. Poorly governed integration can create bidirectional dependencies that amplify failure propagation.
The operator interface, as described in SCADA HMI, must explicitly reflect uncertainty. Suppressing alarm floods or collapsing state transitions to simplify visualization can obscure topology misalignment.
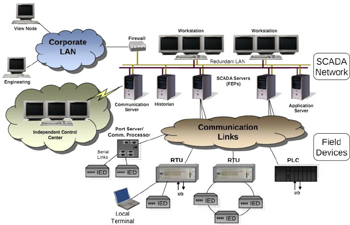
Architectural segmentation enforces trust boundaries between field devices, control networks, and enterprise systems. A flat network design allows lateral movement during intrusion containment.
A structured Grid Cybersecurity Strategy defines firewall placement, identity governance, and intrusion detection, aligning them with operational sensitivity. External advisories, such as DHS and FBI Alerts, reinforce that supervisory systems are strategic targets.
Consider a cascading scenario. A compromised remote access credential alters RTU configuration in a peripheral substation. Communication latency masks configuration drift. The supervisory server replicates outdated breaker status. The automated restoration logic incorrectly isolates the wrong feeder section. DER inverters backfeed into an unintended energized segment with altered protection coordination. What began as a segmentation lapse escalates into equipment damage and an extended outage.
Architecture determines whether such escalation is contained at the boundary or amplified across layers.
Centralized architectures simplify monitoring and patch management but increase dependence on core data centers. Distributed architectures reduce latency and improve resilience but require disciplined synchronization and version control across nodes.
Utilities must decide whether performance headroom justifies governance complexity. If architecture cannot sustain five times nominal event volume and maintain state alignment within tolerance, automation becomes exposure.
Stay informed with our FREE Smart Grid Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
The decision is not an architectural preference. It is whether switching authority remains defensible under forensic review after a disturbance. When control logic executes on an uncertain state, accountability shifts from operator action to architectural sufficiency.
In grid operations, architecture is the last line between the validated state and operational illusion.
Advantages To Instructor-Led Training – Instructor-Led Course, Customized Training, Multiple Locations, Economical, CEU Credits, Course Discounts.
Request For QuotationWhether you would prefer Live Online or In-Person instruction, our electrical training courses can be tailored to meet your company's specific requirements and delivered to your employees in one location or at various locations.