High Voltage Maintenance Training Online
Our customized live online or in‑person group training can be delivered to your staff at your location.

- Live Online
- 12 hours Instructor-led
- Group Training Available
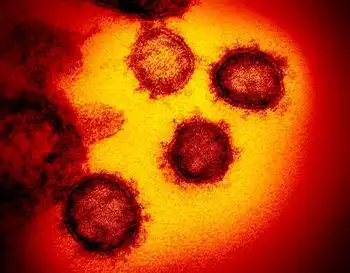
Stuxnet in Iran dominated infections, targeting SCADA malware vulnerabilities at Bushehr and other industrial control systems, suggesting nation-state cyber sabotage or espionage, according to Symantec and security analysts amid regional nuclear tensions.
What This Means
A worm that infected Iran, targeting SCADA controls at industrial sites and raising fears of nuclear sabotage.
- 60% of global infections were in Iran, per Symantec.
- Targets SCADA software in industrial control systems.
- Bushehr said only staff PCs hit; core systems safe.
- Analysts cite likely nation-state backing and espionage.
A computer worm that experts said may have been created by a state did not affect Iran’s nuclear plant or government systems, but did hit computers of staff at the plant and Internet providers, officials said.
A senior official at U.S. technology company Symantec told Reuters that 60 per cent of the computers worldwide infected by the so-called Stuxnet worm were in Iran, prompting speculation that the nuclear power plant may have been targeted, as power plant takeover attempts have shown, in an attempt at sabotage or espionage.
Some Western cyber security companies, such as Symantec, suggested the attack could only have been conducted “with nation-state support”, indicating industrial plants in the Islamic state were the target.
The head of the Bushehr nuclear power plant said the worm had only affected personal computers of staff, although Conficker infections have shown broader risks exist.
“A team is inspecting several computers to remove the malware... major systems of the plant have not been damaged,” Mahmoud Jafari told the official IRNA news agency.
Russia, whose suspected U.S. power-plant hacks have raised alarms, was fiercely criticized by the West for involvement in completing the long-mothballed plant. Moscow says the plant is purely civilian.
Iran’s Telecommunications Minister Reza Taqipour said the worm had not been able to “penetrate or cause serious damage to government systems”, the state-run newspaper Iran Daily reported.
Authorities said Iran had identified some 30,000 Internet providers infected by the Stuxnet worm, blaming Iran’s “foreign enemies for creating the virus”.
Diplomats and security sources say Western governments and Israel view sabotage as one way of slowing Iran’s nuclear work, which the West fears is aimed at building bombs. Tehran says it needs nuclear technology to generate electricity.
The malware attacks software programs that run Supervisory Control and Data Acquisition, or SCADA, systems. Such systems are used to monitor automated plants – from food and chemical facilities to power generators, and experts urge we target power grid hackers to protect such assets.
“The Stuxnet spy worm has been created in line with the West’s electronic warfare against Iran,” the newspaper quoted Mahmoud Liayi, secretary of the Information Technology Council of the Industries Ministry, as saying.
Israel, which is assumed to have the Middle East’s only atomic arsenal, has hinted it could attack Iran’s nuclear facilities if international diplomacy fails to curb the country’s program. Iran refuses to recognize Israel.
Related News
Related News

New Electricity Auctions Will Drive Down Costs for Ontario's Consumers
BC Hydro launches program to help coronavirus-affected customers with their bills

The Phillipines wants nuclear power to be included in the country's energy mix as the demand for electricity is expected to rise.

Current Model For Storing Nuclear Waste Is Incomplete

Hydro One crews restore power to more than 277,000 customers following damaging storms in Ontario

UK must start construction of large-scale storage or fail to meet net zero targets.
Sign Up for Electricity Forum’s Newsletter
Stay informed with our FREE Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
Electricity Today T&D Magazine Subscribe for FREE

- Timely insights from industry experts
- Practical solutions T&D engineers
- Free access to every issue

