Grid Cybersecurity & Protection

Cybersecurity for Utilities Protects Operational Control
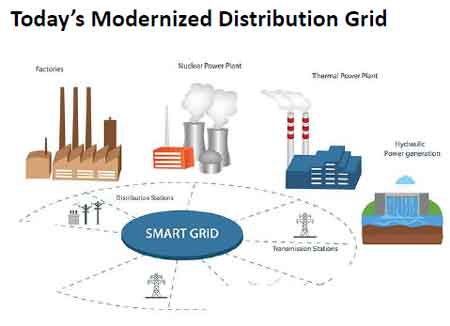
Cybersecurity for utilities protects SCADA, DERMS, substations, and grid communications from unauthorized control, data manipulation, and operational disruption, preserving command integrity, device authentication, and reliable electric system operation.
Electric utilities do not fail because information is lost. They fail when control is compromised. The difference is operational, not theoretical. A corrupted database can be restored. A malicious switching command, executed at the wrong moment, can isolate substations, destabilize feeders, or interrupt service to thousands of customers. Cybersecurity exists to preserve operational authority across grid control infrastructure, ensuring that only authenticated systems and authorized personnel can observe, communicate with, and control…
View more
Latest Grid Cybersecurity & Protection Articles
SADM for ADMS Grid Automation
SADM enables secure automated management of grid devices within ADMS environments by controlling access, updating configurations, and continuously validating device state.
It supports cybersecurity enforcement, SCADA integration, and DER coordination and ensures that automation decisions are based on current field conditions rather than assumed data.
SADM functions as the control layer that determines whether ADMS automation operates on verified device state or outdated field assumptions. It enforces access control, maintains configuration and firmware integrity, and ensures that automation systems operate using verified device data. Without this layer, ADMS relies on device information that may no longer reflect actual field conditions.…
View more
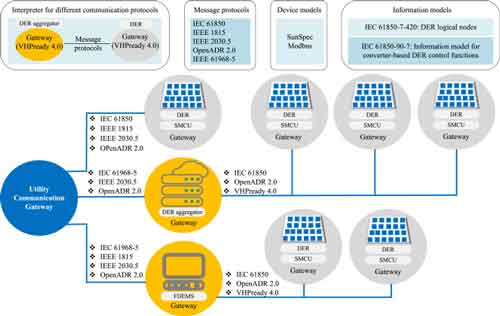
DER Cybersecurity: Protecting Distributed Energy Resources
DER cybersecurity protects distributed energy resources from unauthorized control, protocol manipulation, and data interception across SCADA, DERMS, and grid communications, ensuring secure authentication, encrypted telemetry, and reliable grid operations.
Distributed energy resources introduce a new class of operational risk that traditional utility cybersecurity models were never designed to handle. Unlike centralized generation, DER systems exist at thousands of geographically dispersed connection points—each one communicating continuously with utility control systems, aggregators, and facility controllers. Every communication session becomes a potential control pathway. When those pathways are not properly secured, unauthorized actors can influence grid behavior without ever physically accessing infrastructure.
…
View more

Cybersecurity Analysis for Grid Edge Devices
Cybersecurity analysis in utilities evaluates OT field devices, communication networks, and control systems using threat risk assessment, penetration testing, and protocol validation to identify operational risk, ensure grid reliability, and support secure deployment decisions.
Cybersecurity analysis in utility operations is the process of evaluating field devices, communications, and control systems to determine whether they can be deployed without introducing unacceptable risk to grid reliability, safety, or operational continuity.
In distribution automation environments, this analysis cannot rely solely on IT security methods. Field devices such as reclosers, relays, and sensors operate in real time and directly influence switching actions. A failure…
View more

Automation in Cybersecurity for OT Response and Substation Security
Automation in cybersecurity enables utilities to execute OT device response actions automatically using SIEM and SOAR integration, improving substation security, configuration control, and credential management across multi vendor environments while reducing response time and operational risk.
Automation in cybersecurity is the process of automatically executing security actions across OT devices once a threat is detected, enabling utilities to move from detection to containment without manual coordination between IT and OT teams.
In most utilities, cybersecurity detection happens in the SOC, but execution happens in substations. That separation creates a delay. The SOC can detect a compromised credential, but it cannot…
View more