CSA Z462 Arc Flash Training – Electrical Safety Compliance Course
Our customized live online or in‑person group training can be delivered to your staff at your location.
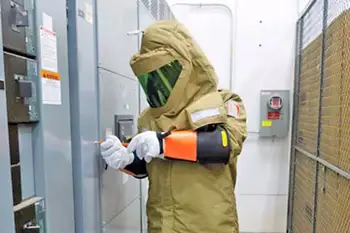
- Live Online
- 6 hours Instructor-led
- Group Training Available
Electrical Grid Cybersecurity fortifies utilities against malware, human error, and remote intrusions using NERC CIP standards, change control, intrusion detection, and defense in depth to protect critical cyber assets and maintain reliable operations.
The Big Picture
Layered protection for utility control systems, aligned with NERC CIP and strong change control to cut cyber risk.
- Focus on basic system integrity and rigorous change control.
- Adhere to NERC CIP-002 through CIP-009 for critical assets.
- Use intrusion detection and continuous monitoring on networks.
- Implement defense in depth with authentication beyond firewalls.
- Address malware vectors, remote access, and human error training.
Cybersecurity is a major threat to utilities' operations, said John Shaw, a senior vice president with Industrial Defender, at the Utilities Telecom Council's annual conference.
As a result, it is essential to protect the nation's electrical grid as rogue forces could use it as a weapon of mass destruction. However, Shaw doesn't believe that most security threats against the electrical grid stems from outside the nation. Instead, security breaches happen at a more practical level.
"It's about basic system integrity, malware coming in over the internet via grid cyber attacks and getting on to a PC that's connected to a [utility's] control system," he said. "There's also just basic mistakes and human error."
In fact, Shaw said cybersecurity strategies should focus on deploying best practices for the smart grid and putting in efficient change control procedures to improve reliability, including adhering to the mandated NERC Standards CIP-002 through CIP-009 that provides a cybersecurity framework for the identification and protection of critical cyber assets.
"That's what security is about," he said. "Every time someone opens a connection they need to close it. It's also about keeping software and operating systems up to date. So we get into issues of data integrity when talking about cybersecurity."
In addition, wireless does not, in itself, make utilities more vulnerable to issues of cybersecurity, Shaw said. Although wireless does create some extent of openness, intrusion detection software protects networks for smart meters and field assets. He said such defense-of-depth strategies are crucial and the use of layered security defenses in an application can reduce the chance of a successful attack. In addition, incorporating redundant security mechanisms requires an attacker to circumvent each mechanism to gain access to a digital asset. For example, a software system with authentication checks may prevent an attacker that has subverted a firewall.
Shaw said defending an application with multiple layers can prevent a single point of failure that compromises the security of the application.
"I don't think wireless by itself or decreases the threat but it does show the critical importance of having multiple layers of security in smarter grid deployments," Shaw said. "In fact, just because [cyber attackers] can get through the physical access layer of wireless, and maybe get through that first encryption layer to a connection point, that should not give them very much power by itself."
Related News
Related News

Altmaier's new electricity forecast: the main driver is e-mobility

Canadian Electricity Grids Increasingly Exposed to Harsh Weather

A Texas-Sized Gas-for-Electricity Swap
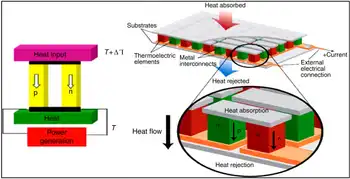
A new approach finds materials that can turn waste heat into electricity

TVA faces federal scrutiny over climate goals, electricity rates

Reconciliation and a Clean Electricity Standard
Sign Up for Electricity Forum’s Newsletter
Stay informed with our FREE Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
Electricity Today T&D Magazine Subscribe for FREE

- Timely insights from industry experts
- Practical solutions T&D engineers
- Free access to every issue
