SADM for ADMS Grid Automation
By Ameen Hamdon, President and CEO, SUBNET Solutions Inc.
By Ameen Hamdon, President and CEO, SUBNET Solutions Inc.
SADM enables secure automated management of grid devices within ADMS environments by controlling access, updating configurations, and continuously validating device state.
It supports cybersecurity enforcement, SCADA integration, and DER coordination and ensures that automation decisions are based on current field conditions rather than assumed data.
SADM functions as the control layer that determines whether ADMS automation operates on verified device state or outdated field assumptions. It enforces access control, maintains configuration and firmware integrity, and ensures that automation systems operate using verified device data. Without this layer, ADMS relies on device information that may no longer reflect actual field conditions.
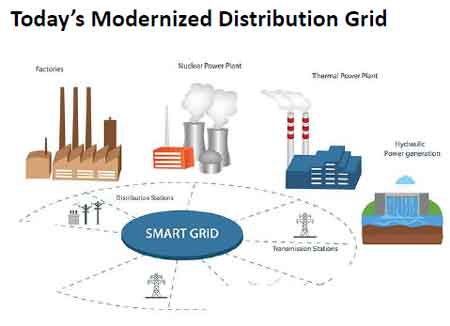
Modern distribution systems now operate thousands of intelligent devices across feeders and substations, often from multiple vendors with different interfaces and capabilities. Each device must be configured, secured, updated, and monitored throughout its long operational lifecycle. Manual processes cannot maintain this level of consistency or accuracy, particularly as device counts continue to increase.
As scale increases, the loss of visibility into actual device state becomes a system level risk. Configuration drift, outdated firmware, and inconsistent access controls expand the cyberattack surface and degrade the quality of data used by automation systems. When device state is not continuously validated, ADMS applications operate under incorrect assumptions, which can lead to unreliable switching decisions, ineffective fault isolation, and restoration actions that do not align with real network conditions.
SADM improves ADMS performance by ensuring that device data reflects actual field conditions. Automation functions such as FLISR and volt var optimization depend on real time data and correct device settings. If device configurations are outdated, automation decisions become unreliable, which introduces operational risk in switching, voltage control, and restoration.

SADM continuously reads and validates device configurations so that ADMS operates using current field conditions rather than assumed engineering values. This closes the gap between system models and actual device behavior.
SADM automates the full lifecycle of grid devices by maintaining continuous control over passwords, configurations, firmware, and operational data. It replaces manual tracking of device state with automated monitoring and update processes that ensure device baselines remain accurate.
This shift removes a major source of human performance risk. Tasks that previously required extensive manual effort, such as collecting device settings or verifying firmware status, are executed automatically and consistently. SADM therefore acts as an operational execution layer for concepts described in automation in cybersecurity, where security and control actions are enforced directly on field devices.
At scale, the operational impact becomes measurable. In one deployment, collecting configuration data from approximately 14,000 devices required weeks of manual effort, while automated collection completed the same task in about four hours. In another case, analyzing 1.4 million fault records manually would require an estimated 35 person years of labor.
Automated data collection enabled immediate analysis and contributed to operational savings approaching $1 million per year. This is not incremental efficiency. It determines whether device management is operationally viable at modern grid scale.
SADM extends cybersecurity from network protection into direct device control. It centralizes authentication and enforces access policies so that engineers interact with devices through controlled processes rather than direct credential access.
This eliminates shared passwords and unmanaged access points, which are common sources of exposure in large scale device deployments. It also ensures that every interaction with a device is logged and auditable.
These capabilities reinforce broader cybersecurity practices for utilities but apply them at the operational level, where devices are configured and controlled. Without this layer, cybersecurity policies remain disconnected from actual device behavior.
Secure remote access alone does not resolve the device management problem. While it centralizes authentication and controls user access, it still depends on manual processes to update passwords, configurations, firmware, and audit records.
This reintroduces inconsistency, increases labor requirements, and leaves gaps between security policy and actual device state. SADM extends secure access into automated execution, ensuring that control, validation, and audit functions are applied continuously across all devices rather than performed intermittently.
Modern grids include a wide mix of devices from different vendors, each with its own configuration tools, password structures, and communication methods. Some devices use modern protocols while others rely on proprietary interfaces, creating fragmentation in how devices are managed.
SADM resolves this by providing a unified control layer that manages all devices regardless of vendor differences. This reduces operational complexity and avoids the need to maintain multiple device management systems.
This challenge becomes more critical as distributed energy resources expand across the grid, increasing both the number and diversity of devices. The risks associated with this expansion are closely related to those described in DER cybersecurity, where distributed assets increase exposure and management complexity.
SADM establishes a continuous loop between field devices and control systems. Devices provide configuration, firmware, and event data to SADM, which validates and maintains an accurate representation of device state. ADMS systems then use this validated data to make automation decisions, while SADM executes controlled updates back to devices when required.
Stay informed with our FREE Grid Cybersecurity & Protection Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
This structure ensures that automation is based on verified data rather than outdated records. A critical constraint emerges here. If device data is not continuously updated, automation performance degrades regardless of how advanced the ADMS algorithms are.
SADM establishes a continuous loop between field devices and control systems. Devices provide configuration, firmware, and event data to SADM, which validates and maintains an accurate representation of device state. ADMS systems then use this validated data to make automation decisions, while SADM executes controlled updates back to devices when required.
This structure ensures that automation is based on verified data rather than outdated records. A critical constraint emerges here. If device data is not continuously updated, automation performance degrades regardless of how advanced the ADMS algorithms are. This failure mode is difficult to detect in real time because the automation logic appears to function correctly while operating on incorrect device inputs.
Utilities implementing SADM must address integration challenges across both legacy and modern devices. Differences in communication protocols, device capabilities, and vendor tools create complexity that must be managed carefully.
There is also a tradeoff between automation and direct control. Increased automation reduces labor and improves consistency, but it requires trust in system governance and validation processes. At the same time, stronger cybersecurity controls may introduce delays in device access, which must be balanced against operational response requirements.
An important edge case occurs when device configurations change outside controlled processes. If these changes are not captured, ADMS may operate under incorrect assumptions, leading to failed switching operations or incorrect restoration decisions.
SADM changes grid operations by shifting device management from periodic manual processes to continuous automated control. Utilities gain confidence that device state is accurate, which improves the reliability of automation decisions.
It also reduces operational costs by minimizing manual effort and field visits. At scale, automated data collection enables advanced analysis and supports predictive maintenance strategies.
The monitoring and validation capabilities of SADM align with the analytical processes described in cybersecurity analysis, but extend them into real time device management and operational decision making.
The key decision is whether device management can remain manual in an environment defined by scale, complexity, and risk. Without automated control and validation, the growth of grid devices will outpace the ability to manage them safely and reliably.
Advantages To Instructor-Led Training – Instructor-Led Course, Customized Training, Multiple Locations, Economical, CEU Credits, Course Discounts.
Request For QuotationWhether you would prefer Live Online or In-Person instruction, our electrical training courses can be tailored to meet your company's specific requirements and delivered to your employees in one location or at various locations.