Buy vs Build Event Correlation Platform for Utility OT Observability
By R.W. Hurst, Editor
By R.W. Hurst, Editor
Buy vs Build Event Correlation Platform decisions define how utilities govern OT telemetry, alarm noise reduction, root cause analysis, and automated remediation under regulatory constraints. Procurement errors can cascade into misoperation risk and false incident escalation.
The procurement decision is not about software preference. It is about where operational accountability resides when correlation logic determines incident priority inside a regulated control environment. In a utility network operations center, event correlation defines whether telemetry becomes actionable intelligence or unmanaged noise.
Modern grid operations generate high volume alarms across SCADA, WAN infrastructure, DER telemetry, cybersecurity systems, and automation platforms. Without structured correlation, Tier 1 operators escalate device alerts rather than service incidents. The decision boundary is whether to externalize that intelligence layer to a commercial platform or internalize it through a custom engineered model stack.
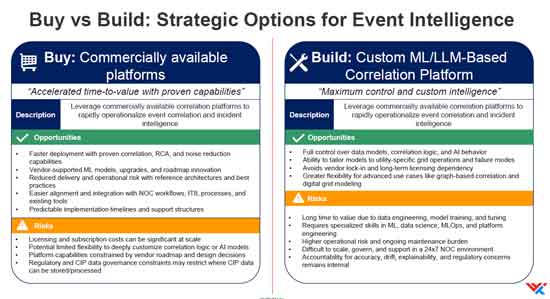
A buy decision accelerates deployment and provides pre-built normalization, topology awareness, and anomaly detection models. A build decision preserves architectural sovereignty and avoids dependency on vendor roadmaps. Both paths introduce operational exposure if threshold discipline, governance structure, and telemetry quality are not explicitly engineered.
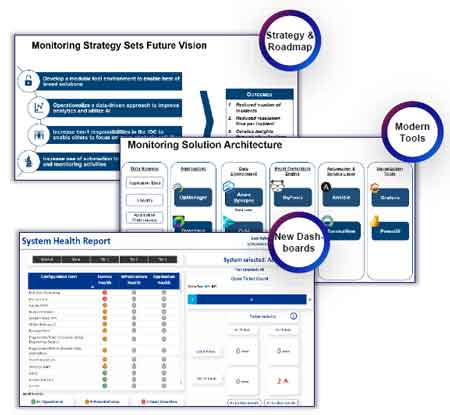
The first procurement axis is time to operational value. Commercial platforms typically ingest multi domain telemetry and begin grouping alarms into correlated incidents within months. In mature deployments, event volume reduction can exceed 60 percent, decreasing Tier 1 cognitive load and reducing false escalation rates. That improvement, however, is bounded by vendor defined correlation logic and model transparency.
A custom build enables tailored graph models aligned to feeder topology, switching states, and protection schemes. Utilities can encode failure modes specific to their grid architecture. Yet internal development requires sustained investment in data engineering, model tuning, explainability, and 24 by 7 operational support. The risk profile shifts from licensing cost to internal capability burden.
Stay informed with our FREE Grid Data Foundations & AI Infrastructure Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
Event correlation does not operate in isolation. It must integrate with the Utility Network Automation Architecture to preserve awareness of switching logic and control authority boundaries. Correlation engines that misinterpret switching events as faults can trigger cascading confusion among operators and inappropriate dispatch actions.
A procurement tradeoff emerges between deployment speed and architectural control. Commercial platforms provide predictable implementation timelines and structured upgrade cycles. Custom builds offer deeper control over correlation logic but introduce lifecycle complexity and staffing dependencies.
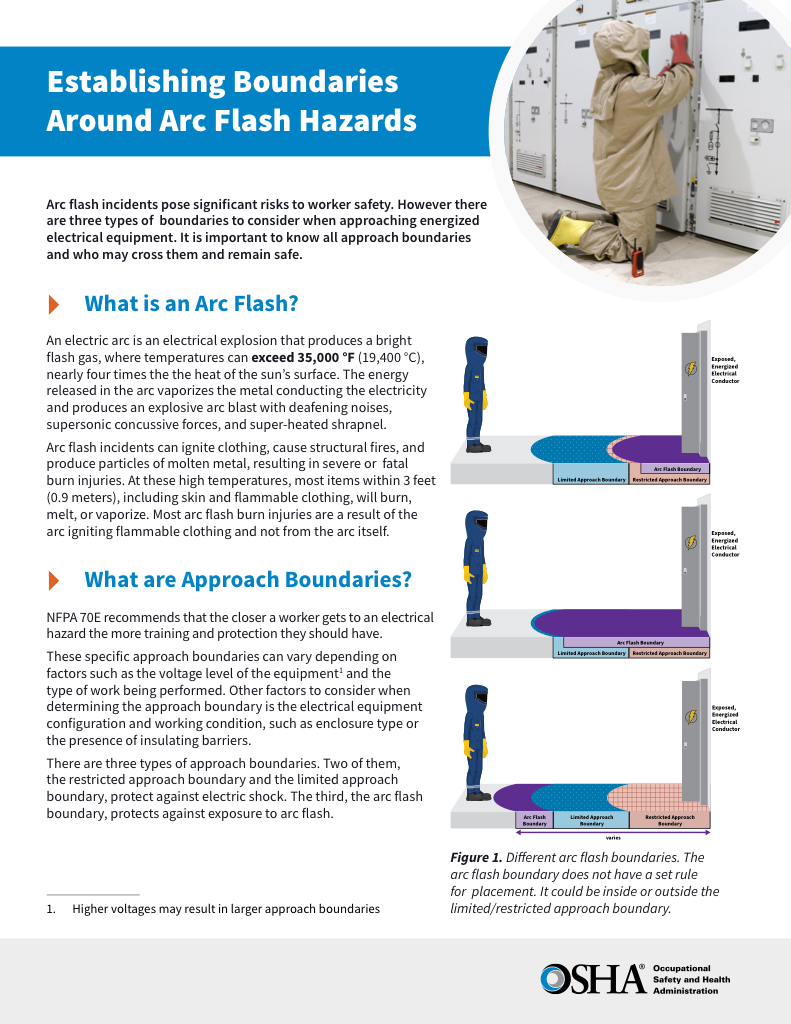
Correlation accuracy is not binary. It is threshold based. Noise suppression, anomaly detection sensitivity, and incident grouping parameters must be tuned to grid conditions. Over aggressive noise reduction can mask early warning indicators. Under tuned thresholds reintroduce alert fatigue.
This governance layer must align with Enterprise AI Governance for Utilities to ensure explainability, auditability, and regulatory defensibility. In regulated OT environments, the inability to justify why alarms were suppressed creates compliance exposure.
Model drift is a deployment constraint often underestimated. As DER penetration increases and telemetry density rises, correlation baselines shift. Without structured feedback loops and incident review cycles, correlation precision degrades. A platform that initially reduced events by 60 percent can fall below 35 percent effectiveness within two years if thresholds remain static.
Consider a scenario where WAN latency alarms, SCADA communication drops, and feeder voltage deviations are incorrectly correlated into a single network incident. If the root cause is misidentified as a telecom fault rather than a protection misoperation, switching crews may be delayed while operators await network remediation. Voltage excursions propagate, reclosers misoperate, and the customer outage scope expands.
That cascading sequence begins with correlation logic. A procurement error at the platform level can translate into grid level operational misjudgment.
Correlation engines must therefore integrate telemetry from Utility WAN Architecture and operational systems while respecting segmentation controls defined in Cybersecurity for Utilities. Cross domain visibility improves root cause identification but increases governance complexity.
An operational edge case arises when inverter based resources inject high frequency telemetry anomalies during cloud transient conditions. These anomalies can resemble patterns of cyber reconnaissance or device malfunctions. If correlation models are trained primarily on legacy synchronous generation telemetry, DER variability may be misclassified as fault behavior.
Integration with DER Cybersecurity and SCADA event streams from SCADA Cybersecurity is necessary to prevent false-positive escalation and unnecessary field dispatch.
Utilities moving toward anomaly detection and automated remediation must also evaluate how correlation integrates with AIOps for Electric Utilities. Automated response introduces a decision gravity boundary: once remediation actions execute without human review, accountability shifts from operator to algorithm.
When correlation based logic drives automated containment, the utility no longer purchases a dashboard. It is delegating incident prioritization authority to a model. That delegation increases regulatory exposure and board level accountability.
Buy decisions centralize risk with vendor supported model updates, but constrain customization depth. Build decisions centralize risk internally and require a formalized MLOps discipline. Neither path eliminates risk. It reallocates it.
A prudent procurement approach often stages deployment. Utilities may buy a commercial aggregation and correlation platform while developing limited custom models for high consequence grid services. This hybrid model preserves rapid operational improvement while containing model complexity within defined use cases.
The unresolved boundary remains threshold governance. Who owns the evolution of the correlation rule as grid topology, DER penetration, and cybersecurity posture evolve? If that ownership is unclear, correlation accuracy becomes episodic rather than structural.
Download our FREE Electrical Training Catalog and explore a full range of expert-led electrical training courses.

Explore 50+ live, expert-led electrical training courses –
