Utility Network Automation Architecture For Deterministic AI Ops
By Matt Deibel, Manager Grid Automation Services, Southern California Edison
By Matt Deibel, Manager Grid Automation Services, Southern California Edison
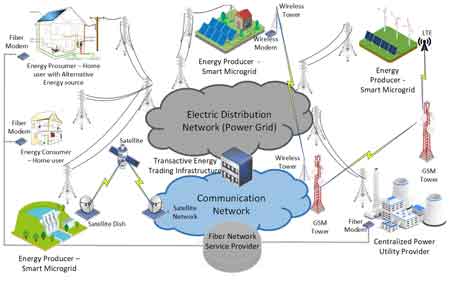
Utility network automation architecture governs deterministic provisioning, config drift control, AI orchestration, and ITSM integrated remediation to prevent unstable switching, audit gaps, and cascading network failures across substations and telecom domains.
Utility network automation architecture is not an IT efficiency initiative. It is an operational control boundary that determines whether telecom and substation networks can be trusted to execute switching, protection coordination, and remote remediation under AI assisted conditions.
In large service territories exceeding 50,000 square miles, with more than 100,000 infrastructure assets and hundreds of substations, manual provisioning and fragmented workflows introduce configuration variance that scales faster than human review capacity can keep up. When device onboarding, DNS updates, IP reservations, and configuration pushes occur across disconnected systems, drift becomes systemic rather than incidental.
The decision problem is singular. Should automation be deployed as isolated scripts, or as a governed architecture that enforces deterministic execution, configuration validation, and audit traceability across the entire network lifecycle?
Utility network automation architecture must operate as a deterministic network management layer that governs both configuration state and the integrity of network data across substations and field devices. It is not merely a management system for ticket execution. It enforces lifecycle control over network features, validates source of truth alignment, and constrains utility network implementation workflows so that topology changes, policy updates, and device onboarding events do not introduce hidden variance into operational control paths.

Onboarding sequences typically include inventory pull, data extraction, application of the configuration template, DHCP reservation, bootfile assignment, and full configuration deployment. In a utility network automation architecture, these steps are orchestrated through a governed workflow engine that enforces state validation before advancing execution.

Determinism is the first control discipline. Machine to machine data entry reduces input variance, but only if source of truth systems are synchronized. If CMDB, IP address management, and configuration repositories diverge by even one field, automated pushes propagate errors at machine speed. A 0.5 percent configuration mismatch across 10,000 endpoints results in 50 latent misconfigurations that can trigger routing asymmetry or firewall rule conflicts.
This synchronization requirement must align with the transport reliability principles described in Utility WAN Architecture, since orchestration integrity depends on deterministic network paths between substations, data centers, and control applications.
The tradeoff emerges between speed and validation depth. Aggressive automation reduces provisioning time from days to minutes, but deeper pre deployment validation increases orchestration latency. Utilities must define the acceptable threshold where reduced time to deploy does not compromise configuration integrity.
Day 2 use cases define the architecture's durability. Patching, software upgrades, regression testing, rollback, config drift detection, interface validation, SLA monitoring, automated threat response, and NERC-aligned enforcement form the operational backbone.
Config drift detection is a model constraint issue. Golden configurations serve as a static baseline, whereas live networks adapt to field conditions, firmware revisions, and regulatory updates. If drift thresholds are too strict, automated remediation can overwrite intentional field adjustments. If thresholds are too loose, silent divergence accumulates.
Continuous enforcement logic must therefore integrate with broader Cybersecurity for Utilities governance models, where segmentation policy, access control, and workflow execution share a common compliance boundary.
The cascading consequence appears when a drift in a substation firewall allows unintended routing between protection zones. That routing anomaly may not trigger immediate alarms. Instead, it reduces segmentation discipline. During a simultaneous DER voltage excursion and remote switching event, telemetry delays combined with misrouted traffic can create operator uncertainty.
DER heavy feeders amplify this exposure, which is why automation logic must remain consistent with DER Cybersecurity controls that govern inverter communications and distributed endpoint trust.
Uncertainty during the transition of authority is an operational risk multiplier.
The transition from automation to orchestration to agentic operations introduces reasoning layers above deterministic workflows. AI agents may recommend remediation when alarm streams exceed 1,000 events per day, with 300 deemed actionable. However, recommendation authority is not execution authority.
Utility network automation architecture must separate reasoning from actuation. AI systems can analyze telemetry, correlate incidents, and propose change requests, but final execution must pass through rule based guardrails, role based access control, logging, and ITSM integration.
This governance boundary aligns with Enterprise AI Governance for Utilities, in which model outputs are gated before they impact OT infrastructure.
Observability and control center visibility must also remain synchronized with network workflows, reinforcing architectural alignment with SCADA Cybersecurity, since telemetry integrity and automation share dependency chains.
Audit ready change tracking and reporting are survivability mechanisms. Every automated workflow must generate traceable artifacts that show the request origin, approval state, configuration delta, and rollback capability.
An operational edge case arises during simultaneous patch deployment and high-load restoration. If automated patching continues while feeder switching is underway, CPU contention or routing instability may degrade SCADA responsiveness. Architecture must include temporal guardrails that pause non critical automation during active grid events.
As orchestration maturity increases, utilities inevitably approach the transition toward Autonomous Utility Networks. The architectural question is not whether autonomy is possible. It is whether deterministic guardrails remain stronger than adaptive reasoning authority.
Stay informed with our FREE Grid Data Foundations & AI Infrastructure Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
The unresolved boundary is not whether to automate. It is how far to delegate authority to orchestration platforms before human review becomes conditional rather than mandatory.
A utility network automation architecture that manages more than 100,000 assets with static headcount delivers measurable efficiency. But if execution authority outpaces governance maturity, error propagation accelerates beyond human capacity to contain.
Automation reduces variance only when architecture constrains it. Without architectural discipline, automation amplifies it.
Explore 50+ live, expert-led electrical training courses –
