Utility NOC Maturity Model for Grid Observability
By R.W. Hurst, Editor
By R.W. Hurst, Editor
Utility NOC Maturity Model defines the staged evolution from reactive monitoring to predictive grid observability and centralized grid intelligence governance in regulated OT environments, where threshold discipline determines operational risk exposure.
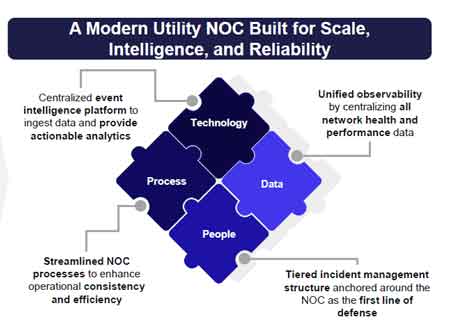
A modern utility Network Operations Center (NOC) is no longer a device alarm clearing function. It is an operational control layer that determines whether telemetry, topology awareness, and remediation authority are aligned to grid risk. The maturity path of the Utility Network Operations Center Maturity Model defines how that control layer evolves under regulatory, cyber, and reliability constraints.
In regulated OT environments, monitoring gaps do not remain informational weaknesses. They become reliability liabilities. When alarm noise masks a protection relay misconfiguration or a WAN latency spike, the consequence is not delayed reporting but potential switching misoperation and cascading feeder impact.
The staged evolution of a modern utility NOC architecture, therefore, reflects increasing observability fidelity, structured incident governance, and centralized grid intelligence capable of supporting predictive intervention rather than reactive dispatch.
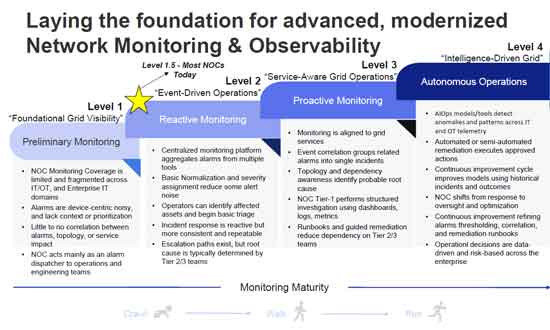
The Utility Network Operations Center Maturity Model progresses through four distinct maturity stages. Each stage shifts the NOC from device centric monitoring toward service aware, risk informed operational governance.
At Level 1, monitoring coverage is fragmented across IT, OT, and enterprise domains. Alarms are device centric and lack service context. Escalation paths exist, but the root cause is typically determined by engineering teams outside the NOC.
The operational constraint at this level is alert fatigue. Thresholds are often static and rarely reviewed. In field assessments, more than 60 percent of alerts may be non actionable, consuming Tier 1 capacity while obscuring true degradation signals.

The deployment tradeoff is between cost and coverage. Expanding telemetry sources without normalization increases noise density and slows triage. Without structured tagging and correlation, adding tools worsens situational clarity.
Level 2 aligns monitoring to grid services rather than devices. Event correlation groups related alarms into single incidents. Topology and dependency awareness identify probable impact scope.
Here, threshold discipline becomes central. Overly aggressive anomaly detection models create false positives that erode operator trust. Conservative thresholds delay incident declaration and extend mean time to containment.
A cascading operational consequence example illustrates the risk. If WAN congestion is misclassified as localized device failure, switching commands may be rerouted manually. That manual intervention can introduce timing variance, resulting in protection coordination stress across adjacent feeders.
This level requires integration with Utility WAN Architecture to ensure network telemetry supports grid service mapping rather than generic availability metrics.
Maturity progression is not abstract. It is built on an event intelligence platform stack that determines whether observability translates into control authority.
At scale, a modern utility NOC architecture typically includes an aggregator layer that ingests alarms and telemetry from IT, OT, and edge domains. That aggregation is not sufficient on its own. Without a structured data pipeline that normalizes tags, timestamps, asset hierarchies, and topology context, downstream analytics inherit ambiguity.
The event correlation layer must group related signals into incident objects that reflect service impact, not device noise. If correlation logic is opaque or poorly tuned, false root cause attribution can propagate through automation workflows.
Automation layers execute remediation under defined authority thresholds. However, automation without service layer validation risks acting on incomplete state awareness. The service layer must map telemetry to grid functions, feeder topology, and protection domains before remediation authority is invoked.
Visualization and analytics platforms complete the stack, providing operators with a common operating picture. If visualization is detached from the correlation and automation layers, the NOC reverts to observational monitoring rather than governed control.
Each layer introduces a control boundary. Weakness in any boundary degrades the entire maturity claim.
At Level 3, anomaly detection extends across IT and OT telemetry streams, and remediation authority begins to shift from manual triage toward governed automation. The NOC transitions into a grid observability center supported by AIOps for Electric Utilities, but this transition introduces new forms of risk.
Model explainability becomes a control issue. If anomaly scoring cannot be traced to deterministic telemetry features, operators cannot defend remediation actions under regulatory scrutiny. Governance alignment with Enterprise AI Governance for Utilities becomes mandatory once the remediation authority extends beyond advisory recommendations. A reduction in mean time to identify incidents is not sufficient if the underlying model logic cannot be audited.
Cross domain telemetry normalization failures create additional friction. IT metrics may report packet loss percentages, while OT devices report status flags or discrete alarms. Without rigorous normalization in the data pipeline and alignment of the architecture with the Utility Network Automation Architecture, correlation engines can misinterpret signal relationships. This produces incidents that appear statistically coherent but operationally misleading.
Incident traceability audit exposure also increases at this stage. When semi automated remediation executes runbooks, the system must preserve a structured chain of evidence showing trigger conditions, decision thresholds, and action outcomes. Without governance boundaries informed by Cybersecurity for Utilities and SCADA Cybersecurity, post incident review may reveal that remediation authority exceeded documented operational controls.
Stay informed with our FREE Grid Data Foundations & AI Infrastructure Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
Quantified authority signals at this stage may include a 30 to 40 percent reduction in mean time to identify incidents and a measurable 20 percent reduction in false positive alerts after correlation tuning. However, these gains are conditional. Model drift, evolving DER penetration, and topology reconfiguration can erode detection fidelity if retraining cycles are not formally governed.
At enterprise scale, even a 1 percent misclassification rate across 20,000 monitored endpoints can generate hundreds of unintended remediation events per year, shifting operational risk from detection failure to automation error.
Level 3 maturity is therefore not defined by tool adoption. It is defined by whether anomaly detection, correlation logic, and remediation authority remain auditable, explainable, and bounded within operational risk tolerance.
Level 4 represents centralized grid intelligence where the NOC transitions from response to oversight and optimization. Automated remediation covers common scenarios under Tier 0 authority. Tier 1 through Tier 3 operate within a structured incident response model supported by unified observability.
At this stage, the NOC operates in coordination with Agentic Operations for Electric Utilities and AIOps for Electric Utilities, while retaining human accountability for grid impact decisions.
The primary model uncertainty at Level 4 involves drift. As load profiles, DER penetration, and switching patterns evolve, anomaly baselines degrade. Without continuous governance anchored in Cybersecurity for Utilities and SCADA Cybersecurity, automation may propagate flawed decisions at scale.
This is where decision gravity increases. If the NOC authorizes automated remediation across thousands of endpoints without validated correlation accuracy, a single misclassified anomaly can propagate operational disruption across multiple substations within seconds.
The unresolved boundary at Level 4 is whether Tier 0 automated remediation authority should extend across transmission substations without deterministic correlation confidence thresholds formally defined in governance policy.
The transition between levels is not purely technological. It requires disciplined process redesign, structured incident tiers, and data architecture capable of supporting event correlation, data lakes, automation, and visualization layers similar to those described in the modernized NOC architecture.
Utilities face a build versus buy tradeoff when implementing event intelligence platforms. Commercial platforms accelerate time to value but may constrain customization and introduce regulatory data residency concerns. Custom development provides full model control but increases operational risk and requires sustained data science capability.
A practical constraint is CIP data segregation. Certain telemetry streams cannot leave controlled environments. This affects architecture decisions and may limit cloud based analytics adoption.
The Utility Network Operations Center Maturity Model does not promise full automation. It defines a staged evolution where observability maturity, governance rigor, and threshold discipline determine whether the NOC reduces grid risk or amplifies it.
Advantages To Instructor-Led Training – Instructor-Led Course, Customized Training, Multiple Locations, Economical, CEU Credits, Course Discounts.
Request For QuotationWhether you would prefer Live Online or In-Person instruction, our electrical training courses can be tailored to meet your company's specific requirements and delivered to your employees in one location or at various locations.