
Protective Relay Training - Basic
Our customized live online or in‑person group training can be delivered to your staff at your location.

- Live Online
- 12 hours Instructor-led
- Group Training Available
Russian Utility Grid Cyberattacks reveal DHS findings on Dragonfly/Energetic Bear breaching control rooms and ICS/SCADA via vendor supply-chain spear-phishing, threatening blackouts and critical infrastructure across U.S. power utilities through stolen credentials and reconnaissance.
What's Happening
State-backed ops breaching utilities via vendors to reach ICS/SCADA, risking grid disruption and control-room access.
Spear-phishing and watering-hole attacks on vendor networks
Stolen credentials used to reach isolated ICS/SCADA
Potential to trigger localized blackouts and service disruptions
Hackers working for Russia were able to gain access to the control rooms of US electric utilities last year, allowing them to cause blackouts, federal officials tell the Wall Street Journal.
The hackers -- working for a state-sponsored group previously identified as Dragonfly or Energetic Bear -- broke into utilities' isolated networks by hacking networks belonging to third-party vendors that had relationships with the power companies, the Department of Homeland Security said in a press briefing on Monday.
Officials said the campaign had claimed hundreds of victims and is likely continuing, the Journal reported.
"They got to the point where they could have thrown switches" to disrupt the flow power, Jonathan Homer, chief of industrial-control-system analysis for DHS, told the Journal.
"While hundreds of energy and non-energy companies were targeted, the incident where they gained access to the industrial control system was a very small generation asset that would not have had any impact on the larger grid if taken offline," the DHS said in a statement Tuesday. "Over the course of the past year as we continued to investigate the activity, we learned additional information which would be helpful to industry in defending against this threat."
Organizations running the nation's energy, nuclear and other critical infrastructure have become frequent targets for cyberattacks in recent years due to their ability to cause immediate chaos, whether it's starting a blackout or blocking traffic signals. These systems are often vulnerable because of antiquated software and the high costs of upgrading infrastructure.
The report comes amid heightened tension between Russia and the US over cybersecurity, alongside US condemnation of power grid hacking in recent months. Earlier this month, US special counsel Robert Mueller filed charges against 12 Russian hackers tied to cyberattacks on the Democratic National Committee.
Hackers compromised US power utility companies' corporate networks with conventional approaches, such as spear-phishing emails and watering-hole attacks as seen in breaches at power plants across the US that target a specific group of users by infecting websites they're known to visit, the newspaper reported. After gaining access to vendor networks, hackers turned their attention to stealing credentials for access to the utility networks and familiarizing themselves with facility operations, officials said, according to the Journal.
Homeland Security didn't identify the victims, the newspaper reports, adding that some companies may not know they had been compromised because the attacks used legitimate credentials to gain access to the networks.
Cyberattacks on electrical systems aren't an academic matter. In 2016, Ukraine's grid was disrupted by cyberattacks attributed to Russia, which is engaged in territorial disputes with the country over eastern Ukraine and the Crimean peninsula. Russia has denied any involvement in targeting critical infrastructure.
President Donald Trump signed an executive order in May designed to bolster the United States' cybersecurity by protecting federal networks, critical infrastructure and the public online. One section of the order focuses on protecting the grid like electricity and water, as well as financial, health care and telecommunications systems.
The Department of Homeland Security didn't respond to a request for comment.
Related News
Related News

South Africa's Eskom could buy less power from wind farms during lockdown
Global Energy War Escalates: Price Hikes and Instability
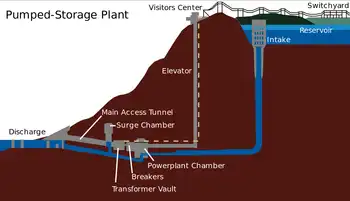
Hydroelectricity Under Pumped Storage Capacity

Shocking scam: fraudster pretending to be from BC Hydro attempts to extort business

Competition in Electricity Has Been Good for Consumers and Good for the Environment

Want Clean And Universal Electricity? Create The Incentives To Double The Investment, World Leaders Say
Sign Up for Electricity Forum’s Newsletter
Stay informed with our FREE Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
Electricity Today T&D Magazine Subscribe for FREE

- Timely insights from industry experts
- Practical solutions T&D engineers
- Free access to every issue

