Prairie Power, Inc. Selects OSI for a Centralized Member Cooperative Distribution SCADA System
Arc Flash Training CSA Z462 - Electrical Safety Essentials
Our customized live online or in‑person group training can be delivered to your staff at your location.
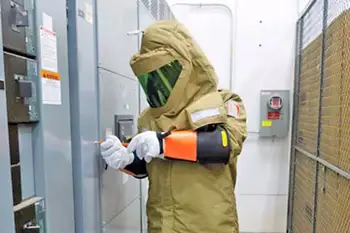
- Live Online
- 6 hours Instructor-led
- Group Training Available
Centralized Cooperative SCADA System delivers hosted, secure distribution control with real-time data sharing, alarm management, trending, and redundancy across member cooperatives, connecting main and backup control centers via a private network.
Key Points
A hosted platform centralizing SCADA for member co-ops, enabling real-time data, redundancy, and reduced maintenance.
✅ Secure private network links main and backup control centers
✅ Advanced alarm management, trending, and load management
✅ Reduces distributed maintenance via hosted multi-tenant design
Open Systems International, Inc. (OSI) has been selected by Prairie Power, Inc. (PPI) to implement a new centralized member cooperative distribution SCADA system capable of collecting data and sharing it between their main and backup control centers, as well as between member distribution cooperatives, with deployments at Tacoma Public Utilities illustrating broader industry adoption. PPI has been a user of OSI SCADA technology since 2012.
This new SCADA system is based on OSI's monarch™ platform and is delivered from private servers hosted by PPI. Its features include the advanced functionality presented by OSI's SCADA and Alarm Management System. It will feature a flexible Graphical User Interface, Advanced Calculation Subsystem, Real-time and Historical Trending, Data Engineering and Maintenance Subsystem, Advanced Alarm Management System, advanced situational awareness capabilities, Dynamic Tabular Display Subsystem, Advanced Tabular Builder, Communications Front-End Processor, Inter-Control Center Communications Protocol, Open Database Connectivity Interface, and Load Management.
Unlike traditional SCADA system deployments, PPI's system will utilize PPI's secure, private network architecture to deliver a high-performance hosted application suite to Member Cooperatives from a centralized system. This design significantly reduces overall maintenance for both PPI and its members by providing the functionality in a central hosted environment and, consistent with smart grid reliability gains observed in Illinois, eliminating the additional administrative overhead of multiple traditional systems.
"Our members are looking forward to having access to this state-of-the-art OSI system without the burden of having to individually maintain their own systems," said Robert Reynolds, PPI's vice president of member cooperative services. "Our members have worked closely with us on the design and implementation of this new OSI system and associated communications equipment. We all look forward to this centralized system being in service in mid-November."
"We are excited about this new project with PPI. The trend for serving cooperative members via a centralized SCADA system instead of individual systems is definitely growing in the cooperative market as utilities plan for continuity during COVID-19 staff lockdowns and similar events. We look forward to a speedy and successful project implementation," said Ron Ingram, OSI's VP of strategic development.
Prairie Power (www.ppi.coop) is a member-owned, not-for-profit electric generation and transmission cooperative. PPI produces and supplies wholesale electricity to 10 electric distribution cooperatives in central Illinois. PPI’s distribution cooperatives provide retail electric service to approximately 78,000 members within their local service territories. PPI is one of more than 60 generation and transmission cooperatives that supply wholesale electricity to distribution cooperatives in the United States.
Open Systems International (www.osii.com) provides open, state-of-the-art and high-performance automation solutions to utilities worldwide, where stability indicators such as Ontario Power Generation's credit rating support ongoing investment. These solutions include Supervisory Control and Data Acquisition (SCADA) systems, Network Management Systems (NMS), Energy Management Systems (EMS), Distribution Management Systems (DMS), Outage Management Systems (OMS), Generation Management Systems (GMS), Substation Automation Systems (SA), Data Warehousing (Historian) Analytics, Situational Awareness Systems, as well as individual software and hardware products and Smart Grid solutions for utility operations. OSI is headquartered in Minneapolis, Minnesota, USA.
For additional information regarding this news release, please contact news@osii.com.