Grid Connectivity and Smart Grid
By William Conklin, Associate Editor
By William Conklin, Associate Editor
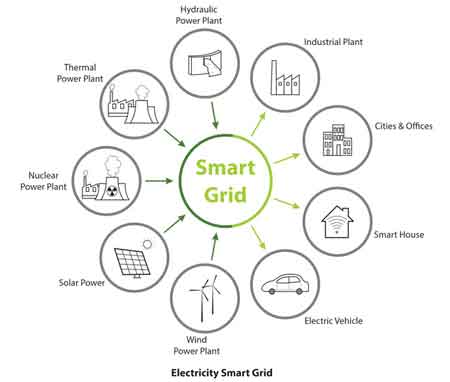
Grid connectivity defines how substations, feeders, DER, storage, and control systems exchange telemetry and switching commands across SCADA networks. Poor topology visibility, latency, or cybersecurity gaps directly increase outage duration, miscoordination in protection, and operational risk.
Grid connectivity is no longer a background IT function. It is a control boundary that determines whether field devices, substations, DER assets, and control rooms operate as a coordinated system or as loosely coupled electrical islands. When topology awareness, latency discipline, and command authentication degrade, restoration confidence collapses.
Utilities once treated communications as a transport layer beneath operations. That separation is no longer defensible. As feeder automation, storage dispatch, and distributed generation scale, grid connectivity defines whether switching sequences execute in the correct order and whether telemetry reflects the actual electrical state.
In high-density distribution environments, connectivity design directly influences outage duration. When breaker status, line sensor data, and DER telemetry arrive out of sequence or not at all, operators default to conservative isolation. Conservative isolation protects equipment but expands customer minutes of interruption. That tradeoff is architectural, not incidental.
Grid connectivity must be engineered as decision infrastructure, not as bandwidth provisioning. OT control rooms depend on deterministic data paths between substations, feeder devices, AMI headend systems, and distributed assets. Without disciplined connectivity governance, SCADA polling intervals stretch, event buffers overflow, and state estimation models drift.
A modern smart electric grid requires synchronized telemetry, validated device identity, and controlled latency thresholds. In deployments with more than 500,000 field endpoints, even a 1 percent telemetry loss rate can mask hundreds of device states during a disturbance window. That is not a reporting defect. It is an operational blind spot.
Download our FREE Electrical Training Catalog and explore a full range of expert-led electrical training courses.

Connectivity architecture must align with SCADA architecture principles, including primary and backup communication paths, failover behavior, and protocol governance. When redundant paths are misconfigured or asymmetrically loaded, failover events can create cascading command delays that outlast the initiating fault.
Consider a mid-feeder fault on a circuit with automated reclosers and sectionalizers. If connectivity latency exceeds relay coordination assumptions, device-to-device confirmation may lag by seconds. Those seconds extend arc duration, increase mechanical stress, and risk miscoordination of protection.
If a recloser closes before upstream state confirmation propagates, fault current can be reintroduced into a partially isolated segment. The result is not merely an extended outage. It is equipment exposure and safety risk.
Grid connectivity determines whether automation compresses restoration time or amplifies the complexity of disturbances. This is the point where architecture becomes accountability.
When it comes to grid connectivity, electric utilities face a persistent trade-off between public carrier networks and private fiber or RF mesh networks. Public networks reduce capital cost but introduce shared bandwidth volatility and dependency on external maintenance cycles. Private networks improve determinism but increase the capital burden and the complexity of lifecycle management.
On high-fire-risk circuits, the tolerance for latency variability narrows. Connectivity thresholds that are acceptable for billing telemetry are unacceptable for adaptive protection schemes. The engineering discipline requires explicit classification of traffic types rather than uniform routing assumptions.
As explored in grid modernization, communications design must be sequenced with protection upgrades and the deployment of automation. Deploying intelligent devices without validating backhaul resilience simply shifts risk from hardware to transport.
State estimation and distribution management platforms rely on a consistent telemetry cadence for grid connectivity. When packet loss or time stamp drift occurs, models interpolate missing states. Interpolation is necessary but not neutral. Beyond certain thresholds, model confidence degrades without visible alarms.
Integration between field devices and SCADA integration must include time-synchronization governance and event-sequence validation. A five-second time skew between feeder sensors can distort oscillography alignment and mislead root cause analysis.
Advanced data analytics can flag anomalies in communication patterns, but analytics do not eliminate transport risk. They surface it after degradation has begun.
DER penetration introduces bidirectional current flow and voltage variability that legacy grid connectivity models did not anticipate. Telemetry compression or prioritization schemes tuned for unidirectional flows can underrepresent reverse-power conditions.
During a localized voltage rise event, delayed DER inverter status reporting can misinform operators about reactive power availability. That delay affects tap changer decisions at the smart substation level and may propagate voltage excursions across adjacent feeders.
Edge computing and distributed intelligence, as discussed in smart grid edge computing, mitigate some latency by localizing decisions. However, distributed logic introduces governance complexity. Firmware consistency, patch discipline, and cybersecurity validation must scale with device count.
Connectivity without security is a structural vulnerability. Control channels must be authenticated, encrypted, and continuously monitored. A compromised remote terminal unit or gateway can inject false state data, triggering incorrect switching sequences.
The necessity of layered defense is reinforced in grid cybersecurity strategy, where identity management, intrusion detection, and segmentation protect operational continuity. Connectivity design must assume adversarial conditions, not just equipment failure.
Grid connectivity is the nervous system of the smart grid. If it is loosely governed, every downstream automation promise becomes conditional. If it is disciplined, latency-bound, and security hardened, automation transitions from experimentation to controlled reliability improvement.
Stay informed with our FREE Smart Grid Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
When evaluating investments, the question is not whether devices can communicate. The question is whether connectivity thresholds are explicitly defined, monitored, and enforced as operational control parameters. That distinction determines whether the grid operates with coordinated intelligence or fragile interdependence.
Explore 50+ live, expert-led electrical training courses –
