DER Cybersecurity: Protecting Distributed Energy Resources
By Grant Gilchrist, P.Eng. Systems Engineer, Grid Modernization Tesco Automation
By Grant Gilchrist, P.Eng. Systems Engineer, Grid Modernization Tesco Automation
DER cybersecurity protects distributed energy resources from unauthorized control, protocol manipulation, and data interception across SCADA, DERMS, and grid communications, ensuring secure authentication, encrypted telemetry, and reliable grid operations.
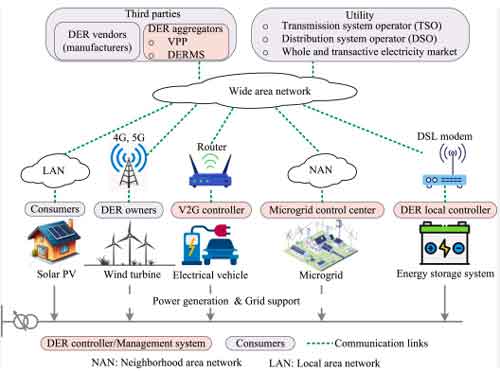
Distributed energy resources introduce a new class of operational risk that traditional utility cybersecurity models were never designed to handle. Unlike centralized generation, DER systems exist at thousands of geographically dispersed connection points—each one communicating continuously with utility control systems, aggregators, and facility controllers. Every communication session becomes a potential control pathway. When those pathways are not properly secured, unauthorized actors can influence grid behavior without ever physically accessing infrastructure.
This risk is not theoretical. Modern DER installations depend on persistent communication with DERMS platforms, SCADA systems, aggregators, and facility energy management systems. These connections enable utilities to manage voltage stability, coordinate load response, and integrate renewable generation safely through centralized control architectures such as a Distributed Energy Resource Management System, which relies entirely on trusted communication with field-connected devices. But they also create a distributed control surface. The cybersecurity boundary is no longer confined to substations or control centers. It now extends to every inverter, gateway, controller, and communication interface deployed across the network.
DER cybersecurity is fundamentally a protocol security problem. The physical equipment itself rarely represents the initial point of compromise. Instead, attackers target the communication protocols that transmit telemetry and control commands between devices and grid operators.
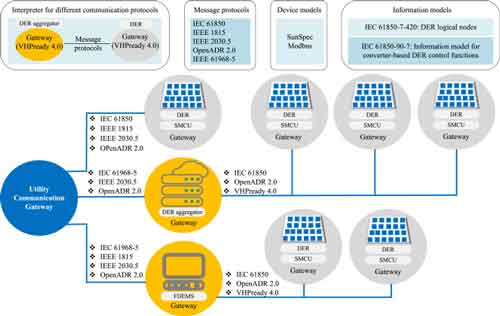
Protocols such as DNP3, IEEE 2030.5, and SunSpec Modbus were developed to support interoperability, device management, and grid integration within modern grid management solutions that coordinate generation, load balancing, and network stability. These protocols enable critical functions, including:
Download our FREE Electrical Training Catalog and explore a full range of expert-led electrical training courses.

• Remote monitoring of DER output and operational status
• Dispatch and curtailment commands from DERMS and SCADA
• Aggregated control through virtual power plant platforms
• Firmware updates and configuration management
Without robust security controls, these same mechanisms can allow malicious actors to inject unauthorized commands, intercept sensitive operational data, or manipulate device behavior.
The transition from isolated industrial networks to IP-based communication dramatically increased exposure. Protocols that were once assumed to operate inside trusted environments now traverse public and semi-public communication infrastructure, often integrating with Advanced Distribution Management Systems (ADMS) that coordinate real-time grid operations. This shift transformed communication protocols into the primary cybersecurity battleground for utility operations.
The central question in DER cybersecurity is deceptively simple: can the grid trust the identity and integrity of communicating devices?
Secure protocols address this problem using layered authentication and encryption. Modern implementations rely on certificate-based authentication and cryptographic verification to ensure that only authorized devices can exchange commands and telemetry. These controls are foundational to cybersecurity for utilities, where maintaining operational trust between distributed assets and centralized control systems is essential to grid stability.
Secure authentication mechanisms prevent unauthorized devices from issuing control commands. Encryption ensures that intercepted communication cannot be altered or understood by unauthorized observers. Message authentication codes verify that data has not been tampered with during transmission.
These protections are essential because DER devices often operate autonomously once deployed. Utilities assume that devices in the field behave as designed. Without continuous identity verification and secure communication, attackers can impersonate legitimate devices or inject malicious commands undetected, potentially corrupting operational telemetry derived from critical infrastructure data sources, such as AMI data, which utilities rely on for real-time grid visibility.
Modern DER communication protocols incorporate multiple layers of cryptographic protection to ensure that device identity and command integrity cannot be forged or manipulated. IEEE 2030.5, for example, uses mutual TLS authentication and certificate-based identity verification supported by Public Key Infrastructure (PKI), ensuring that both utility systems and DER devices authenticate each other before exchanging operational data.
DNP3 Secure Authentication strengthens control system protection by applying message authentication codes, encryption, and role-based access control to prevent unauthorized command injection and privilege escalation. These mechanisms allow utilities to centrally manage trust relationships, revoke compromised credentials, and ensure that only verified devices and authorized operators can issue grid-impacting commands, preserving operational control across distributed infrastructure.
DER assets are expected to remain operational for decades. Communication interfaces installed today will still be transmitting operational data 20 years from now. This longevity creates a unique cybersecurity challenge: security controls must evolve continuously without requiring replacement of physical infrastructure.
Unlike IT systems, which can be refreshed regularly, DER devices often remain in service for extended periods due to their capital costs and operational dependencies. This reality means cybersecurity must be implemented as an adaptable, layered system rather than a static configuration, particularly as utilities deploy increasingly sophisticated grid modeling platforms to simulate and optimize distributed energy integration scenarios.
Secure key management, certificate renewal, and protocol updates allow utilities to strengthen security over time without replacing physical equipment. This flexibility ensures that DER systems remain resilient against emerging threats throughout their operational life.
DER systems rarely communicate directly with utility control centers. Instead, communication typically flows through intermediate systems such as DER gateways, aggregators, and facility energy management systems, which are tightly integrated with broader ADMS vs DERMS operational coordination architectures responsible for managing distributed energy behavior across the network.

These intermediary platforms perform essential operational functions, including:
• Aggregating telemetry from multiple DER assets
• Coordinating response to utility dispatch commands
• Managing local microgrid operations
• Providing secure interface points between utility and customer infrastructure
While these systems improve operational coordination, they also introduce additional cybersecurity responsibility. Each gateway serves as both a control interface and a potential attack vector.
Compromising a single gateway can provide indirect control over numerous DER devices simultaneously. This aggregation effect amplifies cybersecurity consequences, making gateway protection a critical defensive priority.
DER integration depends on continuous, trusted communication between field devices and utility control systems. Secure protocol implementations provide the mechanisms necessary to preserve this trust.
Modern protocol security frameworks incorporate several essential protective capabilities:
• Mutual authentication between devices and control systems
• Role-based access control to limit operational authority
• Encrypted communication channels protecting telemetry and commands
• Certificate-based identity management supporting scalable trust
These capabilities ensure that utilities retain authoritative control over grid-connected resources, even as the number of connected devices expands dramatically.
Without protocol-level security, grid operators cannot distinguish legitimate control commands from malicious ones. Secure communication ensures that operational decisions remain under utility authority, preserving both reliability and safety, especially within critical infrastructure environments governed by comprehensive SCADA cybersecurity protections.
Cybersecurity is no longer a separate IT concern. It is an operational reliability requirement. As distributed resources become embedded into grid operations, communication security becomes inseparable from system stability.
Every DER communication pathway serves both as an operational capability and as a cybersecurity responsibility. Securing those pathways ensures that grid operators retain control authority, maintain system visibility, and prevent unauthorized interference.
The transition to distributed energy has expanded the grid’s physical footprint. DER cybersecurity protects its control integrity.
Without it, the grid remains operational, but no longer fully under the utility’s control.
Explore 50+ live, expert-led electrical training courses –
