CSA Z462 Arc Flash Training – Electrical Safety Compliance Course
Our customized live online or in‑person group training can be delivered to your staff at your location.
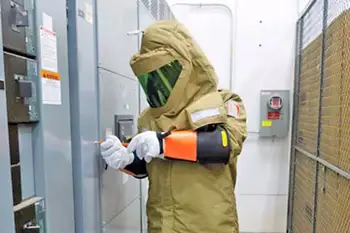
- Live Online
- 6 hours Instructor-led
- Group Training Available
Energy Efficiency Standards face congressional scrutiny as bipartisan rules meet regulatory reform proposals like the REINS Act, risking appliance standards, consumer savings, grid reliability, and pollution cuts secured through transparent review and stakeholder consensus.
What's Behind the News
Federal rules set minimum performance for appliances to cut costs, reduce pollution, and ease grid demand.
Backed by 30 years of bipartisan support and stakeholder input
Proposed REINS Act could delay or block new efficiency rules
Typical households save about $500 annually under current standards
A coalition of energy efficiency groups, trade associations, energy efficiency organizations, environmental organizations, and consumer groups sent a letter to congressional leaders Friday voicing concern about legislative efforts that threaten years of bipartisan, cost-saving rules and standards on energy efficiency.
Bills being considered in the House and Senate would eliminate longstanding checks and balances that ensure thorough review and debate before Congress can eliminate federal regulation implemented appropriately under the law, including bipartisan efficiency standards. Lawmakers are also considering proposals such as the “REINS Act” that could effectively block new standards by adding lengthy, burdensome new steps to the regulatory process, even as energy groups warn of rushed electricity pricing changes, based on arbitrary cost limits that ignore the tremendous net financial gains to consumers from energy efficiency standards.
“We urge you to proceed with caution as Congress considers how best to accomplish broad regulatory reform and debates energy-related tax incentives to ensure that cost-saving energy efficiency standards, which have enjoyed 30 years of bipartisan support, are not put at risk,” the groups wrote in the letter.
The groups signing the letter were the Alliance to Save Energy, American Council for an Energy-Efficient Economy, Appliance Standards Awareness Project, ASHRAE, California Energy Commission, Consumer Federation of America, Copper Development Association, Cree, Environmental and Energy Study Institute, Hannon Armstrong, Midwest Energy Efficiency Alliance, National Consumer Law Center on Behalf of its Low Income Clients, Natural Resources Defense Council, Northeast Energy Efficiency Partnerships, Polyisocyanurate Insulation Manufacturers Association, Southeast Energy Efficiency Alliance, Southwest Energy Efficiency Project, Urban Green Council, and Vermont Energy Investment Corporation.
“Efficiency standards that take years to review, analyze and develop – with extensive involvement and most often the support from the industries and other stakeholders affected – are threatened by these sweeping bills,” Alliance to Save Energy President Kateri Callahan said. “Congress absolutely should review and update regulations where necessary, but it can and should do so under the current rules that already provide meaningful checks and balances. Businesses and consumers need a predictable playing field in which utility rate designs can evolve without being upended every time we have a power shift in Washington.”
The groups said some of these legislative proposals would make it far too easy for Congress to eliminate in one reckless and fell swoop dozens of regulations that have been years in the making.
They cited the “Midnight Rules Relief Act” that recently passed the House and has been introduced in the Senate. It would allow Congress to quickly rescind all regulations finalized since June 13. Among regulations finalized since then are several significant appliance standards, including, dehumidifiers, battery chargers and compressors. Several more standards have been issued but await final administrative approval under the Trump administration as a potential Clean Power Plan replacement is weighed by officials.
“These are not last-minute standards rushed in under the cover of darkness,” said ASAP Executive Director Andrew deLaski. “They were developed over years of transparent public review and stakeholder negotiation. Many of them have broad consensus support from affected industries that have long since adapted to the new rules and don’t want to see them changed.”
“There should be no question about the benefits of efficiency standards. A typical household with products meeting the latest standards is saving about $500 a year,” said ACEEE Executive Director Steven Nadel. “Appliance prices have dropped as the standards have been enacted and consumers have more product choices than ever before. And at the same time, we’ve reduced stress on the grid, significantly cut pollution, and, alongside a clean electricity standard, eliminated the need for expensive new power plants that drive up utility rates.”
Related News
Related News

Electricity sales in the U.S. actually dropped over the past 7 years

A Snapshot of the US Market for Smart Solar Inverters

Power Co-Op Gets Bond Rating Upgrade After Exiting Kemper Deal

Scatec Plans EGP 5 Billion Grid Investment to Evacuate Egypt Solar Power

Windstorm Causes Significant Power Outages

Russia-Ukraine Agreement on Power Plant Attacks Possible
Sign Up for Electricity Forum’s Newsletter
Stay informed with our FREE Newsletter — get the latest news, breakthrough technologies, and expert insights, delivered straight to your inbox.
Electricity Today T&D Magazine Subscribe for FREE

- Timely insights from industry experts
- Practical solutions T&D engineers
- Free access to every issue

